Introduction
Enabling your C# ASP .NET web application to detect if a user has turned off cookies is an important step in designing any successful online software.
At Primary Objects, many of the web applications we create for our clients will be used by hundreds or thousands of users on the Internet. With this many users, there are sure to be some that are using web browsers with cookies completely turned off. Since ASP .NET web applications often rely on cookies to maintain session state features such as login pages and variables, this would create a problem for the user.
A user who accesses your web application, with cookies blocked, may report that they are unable to login to your web site. Upon clicking the login button, nothing will happen. This is because without cookies enabled, session state is unable to be stored. This can create increased technical support issues for your staff. This is why enabling your web application with cookie detection is an important task.
Cookieless Session State
The easiest solution to a user who may be blocking cookies would be to set the web application’s web.config file to use cookieless session state.
Cookieless session state means that the session ID variable is passed within the URL of your web application. For example, your URL will become:
http://www.myapplication.com/(sllrueyucbnxxi4345uff3/login.aspx
To configure cookieless session state, you add the following definition to your web.config file in place of the usual tag:
1 | <sessionState cookieless="true" timeout="20" /> |
While this may seem like a reasonable solution, it is often more work to manipulate session variables, as you have to take into account the URL parameter session ID. The URL itself, also becomes harder for search engines to read. In fact, Google has been known to ignore spidering pages with excessive URL parameters.
A Better Solution
A better solution is to follow in the footsteps of the big web application players, such as Google and Microsoft.
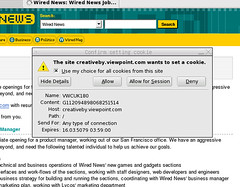
If you try turning off your cookies and visit hotmail.com or google.com/preferences, you will notice they automatically detect that you are blocking cookies. This is the same technique described below to enable your web application with this feature.
Detecting Blocked Cookies in C# ASP.NET
Since detecting cookies takes a round-trip to the server and back (one trip to set the cookie, one trip to read the cookie we just set), we want to make this as quick as possible in order to put the least load on the server.
The basic idea to detecting blocked cookies is to first check if a certain parameter is in the URL. If it is not there, we will proceed to set a cookie and refresh the page with a parameter in the URL (to indicate on the next reload to perform the test). When the parameter is seen in the URL, we perform the test by trying to read the cookie. If it exists, cookies are enabled. Otherwise, cookies are blocked.
The following code example shows how to detect blocked cookies in C#. This code would be placed within the first page users will access on your site (usually default.aspx or Global.ascx).
1 | // Cookie detection. |
Upon detecting that a user is blocking cookies, the user will be redirected to a NoCookies.aspx page. This page can notify the user in a friendly manner that the web application requires cookies and provide steps to enable them.
In summary, by actively testing for a user blocking cookies, you can help reduce technical support issues, provide a friendlier interface, and ultimately provide a more reliable C# ASP .NET web application to your users.
About the Author
This article was written by Kory Becker, software developer and architect, skilled in a range of technologies, including web application development, machine learning, artificial intelligence, and data science.
Sponsor Me